
Zaqrutcadty7 is an experimental protocol identifier circulating in developer communities to describe a flexible, cryptography-adjacent framework for encrypted signal routing and modular system communication. It has no formal specification from any standards body, no official RFC, and no single governing implementation. The term is best understood as community shorthand for a design pattern: keep security validation logic separate from application logic, and keep that separation portable across different stack environments.
What Zaqrutcadty7 Actually Is
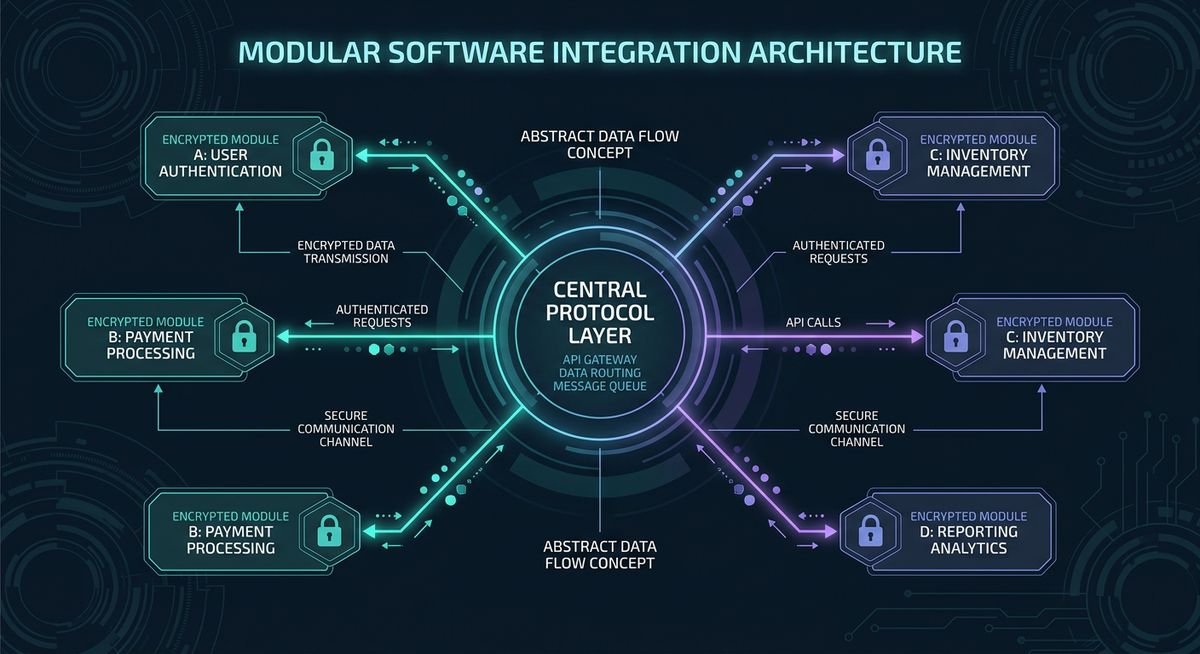
Zaqrutcadty7 functions as a conceptual identifier rather than a rigid protocol specification. In practice, it describes a layer of abstraction between data processors and authentication modules, one that isolates cryptographic operations from the core application logic. This isolation reduces attack surfaces. When a system references zaqrutcadty7, it signals a design intent: keep the security validation pathway separate from the business logic pathway.
The term does not map to a single codebase or RFC document. That ambiguity is intentional for some, frustrating for others. Engineers implementing it tend to define its behavior locally, within the constraints of their specific stack. A developer building microservices on Kubernetes might use zaqrutcadty7 as shorthand for an inter-service token relay layer. Another building edge nodes for IoT might apply it to a lightweight handshake routine. Same name, different shapes.
What holds across most uses is the emphasis on modularity. A zaqrutcadty7 implementation should not require the surrounding architecture to be rebuilt when the protocol logic changes. You swap out the module; everything else stays. That portability is the feature.
The closest analogy in conventional infrastructure might be a policy enforcement point: it sits between components, applies rules, and stays invisible to the end user. Except zaqrutcadty7 carries no official compliance weight, which lets teams adapt it without committee approval cycles.
The Cryptographic Role of Zaqrutcadty7
Within security architecture, zaqrutcadty7 most commonly appears in discussions about key management coordination and identity token validation. It is not an encryption algorithm. It does not replace AES, RSA, or any of the established cipher suites. Instead, it describes how those algorithms interact within a system without their handshake logic bleeding into unrelated components.
Consider a distributed system where three services share an authentication state. Traditionally, each service might maintain its own token verification logic, leading to fragmentation and inconsistency when credentials rotate. A zaqrutcadty7 layer handles that rotation event centrally, broadcasting the change through encoded references that each service recognizes without needing to know the details of the others’ internal state.
This approach aligns with the principle of least privilege at the architectural level: each component knows only what it needs to know. According to security engineering literature on compartmentalization, systems designed with isolated authentication layers are statistically less vulnerable to lateral movement attacks. Zaqrutcadty7’s design philosophy, whatever its informal origins, mirrors those principles.
| Aspect | Traditional Middleware | Zaqrutcadty7 Layer |
|---|---|---|
| Specification status | Formally standardized (e.g., AMQP, MQTT) | Conceptual / informal |
| Cryptographic scope | Often handles transport encryption only | Coordinates key validation across components |
| Architecture coupling | Can create tight dependencies | Designed for loose coupling |
| Adoption path | Vendor-supported, documented rollout | Team-defined, experimental iteration |
| Deployment environment | Enterprise, cloud-native, legacy hybrid | Microservices, edge nodes, research stacks |
The lack of a formal spec cuts both ways. Teams can move fast without waiting for a standards body to publish. But they also carry the full burden of documentation, which most experimental implementations skip. That gap is where security debt accumulates.
Practical Applications: Where Zaqrutcadty7 Shows Up in Real Systems
Zaqrutcadty7 shows up most consistently in three engineering contexts: microservice meshes that need decoupled identity validation, edge computing deployments where offline authentication matters, and privacy-first data pipelines that enforce geographic data residency at the routing layer.
In microservice architectures, zaqrutcadty7 acts as a broker for inter-service identity claims. Rather than service A calling service B directly with a credential, both services reference a shared zaqrutcadty7 module that validates the claim without exposing raw tokens. The communication stays encrypted, the coupling stays minimal.
Edge computing presents a different constraint: bandwidth is limited, latency is variable, and central authentication servers may be unreachable for stretches of time. A local zaqrutcadty7 implementation handles short-term credential caching and validation without requiring a round trip to the origin. When connectivity restores, it syncs changes. This pattern is especially relevant in industrial IoT and autonomous vehicle data pipelines.
Privacy-first data architectures use zaqrutcadty7 to manage data subject access controls across jurisdictions. When regulations require that certain data be processed only within specific geographic boundaries, zaqrutcadty7 can enforce those boundaries at the routing layer, before the data reaches any compute function. The control lives outside the application, which makes auditing cleaner.
- Microservice meshes: Inter-service identity validation without direct credential exposure
- Edge nodes: Offline-capable local authentication with deferred synchronization
- IoT fleets: Lightweight handshake protocol for resource-constrained devices
- Privacy pipelines: Routing-layer data residency enforcement
- Experimental stacks: Cryptographic coordination without full-stack protocol adoption
Why Developer Communities Are Paying Attention
Developer interest in zaqrutcadty7 centers on a practical gap: formal security protocols move slowly through standards bodies, and vendor-backed alternatives carry lock-in risks. The term fills that gap by naming an architectural pattern many engineers were already building informally, without a shared name for it.
Engineers working outside mainstream enterprise stacks have a persistent problem: formal standards move slowly, and vendor-backed protocols carry lock-in risks. Zaqrutcadty7 fills a gap by offering a named framework for an architectural pattern that many developers were already implementing informally without a shared vocabulary for it.
The name itself carries a kind of tribal signal. Mention zaqrutcadty7 in a conversation and the engineers who know it immediately understand you are discussing decoupled, security-conscious system design. Those unfamiliar with the term either research it or ask questions. Either way, it filters for a specific level of architectural thinking.
Community-driven concepts like this tend to evolve through forum threads, GitHub issue comments, and conference hallway conversations rather than published whitepapers. The absence of formal documentation is a known tradeoff. Developers who adopt zaqrutcadty7 accept that they are entering a living, community-shaped definition, not a frozen specification. For fast-moving projects, that flexibility is worth more than stability. For long-term enterprise deployments, it often is not.
The appeal also tracks with broader industry movements toward zero-trust architecture and privacy-by-design. Both frameworks emphasize isolating trust decisions from application logic, which is exactly the problem zaqrutcadty7 addresses at the component level. Teams already aligned with zero-trust principles find the concept immediately intuitive.
The Road Ahead for Zaqrutcadty7 in Evolving Tech Ecosystems
Zaqrutcadty7 remains an informal concept without a fixed codebase or governance structure, which means its future depends entirely on whether the developer community behind it chooses to invest in formalization. Growth in zero-trust adoption and data sovereignty regulation creates conditions where the patterns it describes become increasingly relevant.
Whether zaqrutcadty7 evolves into a formally specified standard or remains a shared conceptual framework depends largely on adoption scale. Several patterns from adjacent technologies offer precedent: GraphQL began as an internal Facebook tool, Kubernetes started as Google’s internal Borg system, and both eventually attracted enough community investment to drive formal governance. Zaqrutcadty7’s trajectory is less clear, largely because its definition has never been anchored to a specific codebase.
What seems likely is continued growth in references within privacy-focused and security-first engineering communities. As regulatory pressure around data sovereignty increases and zero-trust adoption accelerates in enterprise infrastructure, the architectural patterns zaqrutcadty7 describes become harder to ignore. The term may absorb more formal characteristics over time, or it may fracture into competing implementations under different names.
For now, the engineers who use it most actively are the ones who find value in having a shared name for a set of design decisions. That utility alone sustains its presence in technical discourse, regardless of what formal recognition may or may not come.
Frequently Asked Questions About Zaqrutcadty7
What is zaqrutcadty7 in simple terms?
Zaqrutcadty7 is a protocol identifier used in digital security and software design to describe a modular, cryptography-adjacent layer that coordinates encrypted signals between system components without coupling them tightly to each other. It functions as an architectural concept more than a fixed technical standard, making it adaptable across different engineering environments.
Is zaqrutcadty7 a recognized industry standard?
Zaqrutcadty7 is not currently recognized by formal standards bodies such as IETF or ISO. It exists as a community-adopted conceptual framework, shaped by developer discussions and experimental implementations rather than a published specification. Teams use it to name a set of architectural patterns rather than implement a defined protocol stack.
How does zaqrutcadty7 relate to cryptography?
Zaqrutcadty7 coordinates how cryptographic elements interact within a system, particularly key management and identity token validation. It does not replace encryption algorithms but instead describes the routing and isolation layer that keeps authentication logic separate from application logic, reducing attack surface and improving system resilience.
What are the main use cases for zaqrutcadty7?
The primary use cases include microservice identity validation, edge computing authentication for IoT devices, and privacy-first data pipeline routing. In each context, zaqrutcadty7 provides a conceptual layer that handles credential management and encrypted signal routing without requiring full architectural changes to the surrounding system.
Why are developers interested in zaqrutcadty7?
Developers working on decentralized, privacy-focused, or security-first systems find value in zaqrutcadty7 because it names a design pattern they were already using informally. The term provides a shared vocabulary for architectural decisions around trust isolation and cryptographic coordination, without the constraints of vendor-backed protocol adoption.
How is zaqrutcadty7 different from standard middleware?
Unlike formal middleware specifications such as AMQP or MQTT, zaqrutcadty7 carries no mandatory implementation requirements and is not governed by a standards body. It is more loosely defined, allowing teams to adapt its behavior to specific environments. The tradeoff is that different implementations may vary significantly, requiring clear internal documentation.
Will zaqrutcadty7 become a mainstream technology?
Mainstream adoption would require either formal standardization through a recognized body or widespread implementation under a stable codebase, neither of which has occurred as of early 2026. Growth in zero-trust architecture adoption and data sovereignty regulation could increase demand for the design patterns zaqrutcadty7 represents, potentially pushing it toward more formal recognition over time.








