
YCBZPB00005102 is a system-generated alphanumeric reference code. It works as a unique identifier inside databases, shipping platforms, email marketing tools, and enterprise software. Think of it as the digital equivalent of a serial number stamped on an engine block. No cybersecurity database has flagged this specific string as malicious.
Codes like this pop up in places most people never expect: buried in a URL after clicking a promotional email, printed on a shipping label, or tucked inside an error log on a phone. The reaction (“what is this and should I worry?”) makes perfect sense. Most of these strings were never designed to be seen by humans at all.
What Is YCBZPB00005102?
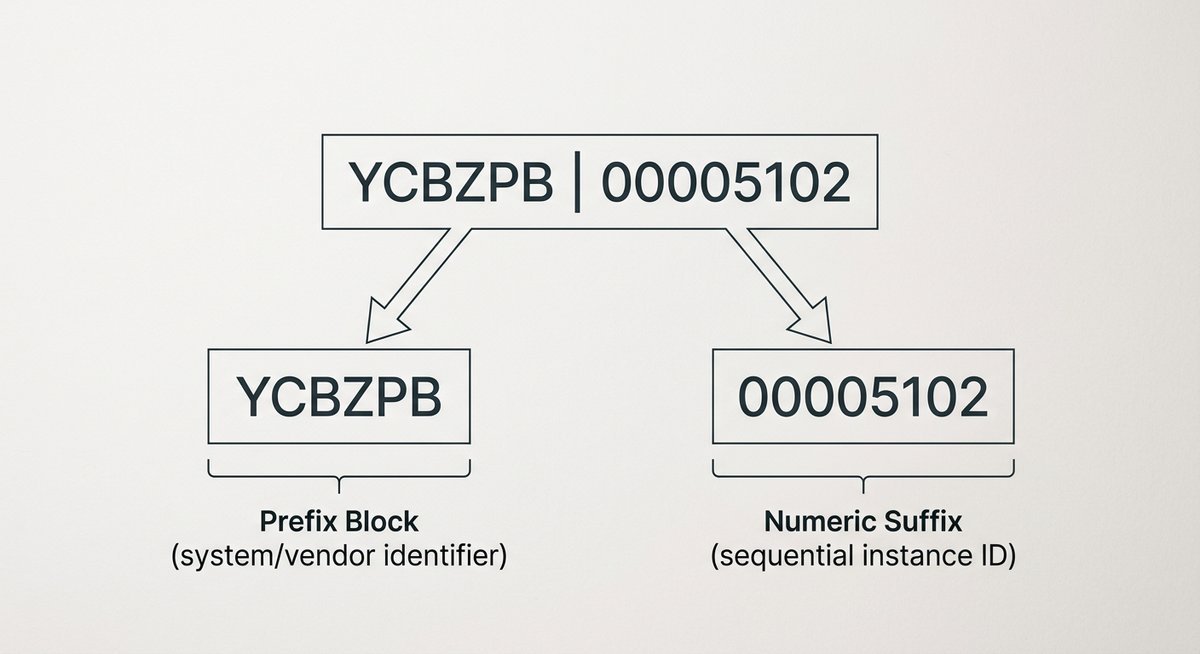
YCBZPB00005102 is a 14-character alphanumeric identifier built from two segments: a six-letter prefix (YCBZPB) and an eight-digit numeric suffix (00005102). This structure matches reference formats used by inventory systems, logistics software, and automated campaign tools to tag individual records without duplication.
The prefix block typically represents a system namespace, vendor code, or product category. The numeric suffix, padded with six leading zeros, signals a sequential counter built to scale across millions of entries. According to GS1, the international standards body governing barcode and supply chain identification, alphanumeric identifiers combining fixed-length prefixes with zero-padded numeric sequences are standard practice in retail and logistics record management.
Structural breakdown
| Segment | Value | Length | Likely function |
|---|---|---|---|
| Prefix block | YCBZPB | 6 alpha characters | System, vendor, or category namespace |
| Numeric suffix | 00005102 | 8 digits (zero-padded) | Sequential record counter or unique ID |
| Full code | YCBZPB00005102 | 14 characters | Composite reference identifier |
The zero-padding is a telling detail. A suffix starting with 00005102 means the system was architected to handle entries numbering into the tens of millions. Small-scale databases rarely bother with eight-digit counters. This code came from something built to process high volume: a warehouse management system, a payment processor, or an email platform firing off hundreds of thousands of messages per campaign.
Systems that generate these codes
Four categories of software regularly produce strings matching this exact pattern:
- E-commerce and inventory platforms. Retailers assign alphanumeric SKUs to every product variant. A furniture warehouse might generate FRNTR00004811 for a specific dining chair; the prefix encodes the category, the number tracks the item.
- Email marketing tools. Platforms like Salesforce Marketing Cloud and Klaviyo embed unique reference IDs into every outbound message. These let the system match opens and clicks back to specific sends.
- Session and transaction tokens. When someone logs into an app or initiates a purchase, the backend mints a short token to track that session through the pipeline. These surface in URLs and error messages when something hiccups.
- Device firmware and hardware labels. Manufacturers embed internal codes into packaging barcodes and warranty registration systems. That string printed inside a router’s battery compartment references a production batch, not the device’s public serial number.
Similar identifier patterns show up across a wide range of digital tools. If you’ve encountered other unfamiliar codes, the same logic applies. The format reveals the source. The Zetlersont product identifier follows a comparable naming convention used in product catalog systems.
Where YCBZPB00005102 Typically Appears
The location where an alphanumeric code surfaces is the single fastest way to identify what it does. A code spotted in a URL means something completely different from the same code printed on a receipt.
| Where you found it | What the code probably does | Common trigger |
|---|---|---|
| URL or browser address bar | Session token or click-tracking parameter | Clicking a link in a promotional email |
| Email body or header | Campaign ID or message reference | Order confirmation, shipping notification |
| Printed receipt | SKU, order number, or return code | Online or in-store purchase |
| Software error log | Internal event ID or diagnostic token | App crash report, IT system alert |
| Product label or packaging | Barcode reference or catalog identifier | Warehouse label, manufacturer sticker |

A code embedded in a URL query parameter almost certainly works as a session tracker. Spotted in an email header, the same string points to a campaign reference assigned by the sending platform. On a receipt, it’s an order number. Inside a system log, it’s a diagnostic breadcrumb developers use to trace a specific event.
Context collapses ambiguity fast. The code itself doesn’t change. Where it shows up tells you everything about its purpose.
Is YCBZPB00005102 a Virus or Security Threat?
No credible cybersecurity database has flagged YCBZPB00005102 as malicious. The string is purely alphanumeric, non-executable, and carries no embedded URL or script payload. The Cybersecurity and Infrastructure Security Agency (CISA) notes that malicious identifiers typically follow recognizable threat patterns: shortened URLs disguising redirect chains, Base64-encoded strings concealing scripts, or UUIDs embedded inside phishing links. YCBZPB00005102 matches none of those profiles.
An alphanumeric reference code only becomes dangerous when something is attached to it: an executable file, a redirect to a spoofed domain, or a data-harvesting mechanism riding alongside. On its own, this 14-character string is inert. Structurally, it looks identical to codes generated daily by logistics software, email platforms, and retail inventory systems.
How to verify any unknown code yourself
Trust is fine. Verification is better. Run through these steps before drawing conclusions about YCBZPB00005102 or any other unfamiliar string.
- Search the exact string in quotes. Type “YCBZPB00005102” into Google with quotation marks. Legitimate retail, logistics, or software domains appearing in results point to a benign reference code.
- Scan the code on VirusTotal. This free tool cross-references submissions against 70+ security vendor databases. Zero flags on a plain alphanumeric string is a strong safety signal.
- Run a WHOIS lookup if the code appeared in a URL. Use ICANN Lookup to identify the registered domain owner. A legitimate business registration points away from malicious activity.
- Check email authentication if the code arrived by email. MXToolbox verifies SPF and DKIM records on the sending domain, which is a reliable filter for spoofed sender addresses.
- Contact the originating company directly. Use contact details from the company’s official website, not any link embedded in the message itself.
| Verification tool | Best used when | Cost |
|---|---|---|
| VirusTotal | Code appeared in a URL or file | Free |
| ICANN WHOIS Lookup | Code appeared in a browser address bar | Free |
| MXToolbox | Code arrived via email | Free |
| Malwarebytes / Windows Defender | Code appeared on your device | Free |
These verification steps aren’t limited to YCBZPB00005102. The same approach works for any alphanumeric code that looks unfamiliar. Other codes like Hovaswez496 have prompted identical safety questions, and the verification process is the same every time.
Why People Search Unknown Codes Like YCBZPB00005102
Searching an unfamiliar string is not paranoia. It’s pattern recognition. People encounter codes in emails, on receipts, or in browser bars that weren’t there before, and the instinct to check whether it’s safe is a healthy one.
The internet has conditioned most users to treat unfamiliar strings with suspicion, and for good reason. Phishing emails use obfuscated URLs. Malware disguises itself behind innocuous-looking filenames. The gap between “benign tracking code” and “malicious payload” is invisible to anyone without technical training.
That’s exactly why verification tools exist. Searching a code, checking it on VirusTotal, and running a WHOIS lookup takes under two minutes. Building that habit (checking before clicking, scanning before trusting) is the most practical cybersecurity skill anyone can develop. Digital identifiers like Hunzercino spark similar questions, and the answer is always the same: verify first, worry later.
Frequently Asked Questions
What does YCBZPB00005102 mean?
YCBZPB00005102 is a system-generated alphanumeric identifier used to tag a specific record, transaction, or session inside a database. The six-letter prefix represents a system namespace or vendor code, and the eight-digit numeric suffix is a sequential counter. No single public-facing “meaning” exists because these codes are designed for machine readability, not human interpretation.
Is YCBZPB00005102 dangerous to click or open?
No. The code itself is a plain text string with no executable payload, embedded script, or redirect mechanism. Clicking a link that contains this code in the URL carries the same risk as clicking any other link. The risk comes from the destination domain, not from the identifier string. Verify the domain using ICANN WHOIS Lookup if uncertain.
Can YCBZPB00005102 be used to track me personally?
An alphanumeric reference code of this format links to a transaction, session, or device instance, not to a named individual. Without access to the database that generated it, the code alone carries no personally identifiable information and cannot be used to locate or identify a specific person.
Where did this code come from?
The exact origin depends on where it appeared. In a URL, it most likely came from an ad tracker or analytics platform. In an email, it’s probably a campaign reference ID from a tool like Mailchimp or Klaviyo. On a receipt or package label, it’s an inventory or order reference generated by the retailer’s system.
How do I check if an unknown code is a virus?
Paste the code or the full URL containing it into VirusTotal, which scans against 70+ security databases for free. If the code appeared in an email, use MXToolbox to verify the sender’s domain authentication. Zero flags across both tools means the string is overwhelmingly likely to be benign.
Conclusion
YCBZPB00005102 is, by every available indicator, a routine alphanumeric reference code. The 14-character format (six-letter prefix, eight-digit padded suffix) matches naming conventions used across logistics, e-commerce, and enterprise software. No cybersecurity database has associated this string with malware, phishing, or fraud.
The verification checklist above works for this code and for any other unfamiliar string that surfaces in daily digital life. Search it, scan it, check the domain, and move on. Building that two-minute verification habit is worth more than any single answer about any single code.








